Payment fraud is not always a problem of detection. Increasingly, it’s a problem of uncertainty.
Modern payment environments are defined by constant behavioral change: new devices, new payment methods, new geographies, and new user patterns appearing faster than historical data can stabilize them. Fraud systems were designed to operate in this reality by translating uncertainty into action; situations where available signals are incomplete and decisions must be made before proof materializes. When confidence is high, transactions proceed. When confidence is low, the system intervenes.
What has changed isn’t the presence of uncertainty, but where the system needs to send it.
Most fraud systems lack a way to express partial confidence or unresolved ambiguity. As a result, uncertainty has only one place to go: suppression. In this context, suppression isn’t a strategy so much as a default response when uncertainty can’t be expressed in any other way. As a result, transactions are delayed, stepped up, or declined, not because fraud has been detected, but because the system can’t be confident enough to proceed.
This behavior is rarely framed as a decision. It appears as caution, conservatism, or maturity. In practice, it is a structural limitation: when systems can’t establish confidence early, legitimate participation is often blocked before proof of trust or risk ever exists.
Detection remains necessary, but in mature systems, it’s no longer the limiting factor. In this report, we’ll explore how this shift quietly reshapes outcomes across payment ecosystems, drawing on original consumer research, real-world transaction data from peak volatility periods, and behavioral analysis across multiple payment contexts. It explores why suppression before proof becomes most visible in mature fraud programs, and what that reveals about the kinds of systems modern commerce now demands.
The mental shift: What holds a system together before proof
To understand what breaks under uncertainty, it helps to name what stabilizes a system when proof doesn’t exist. That stabilizing force is often described imprecisely or avoided altogether because it is easy to confuse it with belief or blind approval. We refer to that stabilizing capacity as trust.
Trust isn’t proof. It’s not certainty. And it’s not the absence of risk. Trust is the mechanism that holds a system together before proof exists.
Trust is a system property, not a judgment. Unlike reputation or velocity, it doesn’t depend on repeated conformity within a narrow behavioral frame. It describes a system’s ability to maintain continuity of decisioning as surface-level behavior changes. It allows confidence to degrade gradually rather than collapse instantly, giving uncertainty somewhere to exist without forcing an immediate verdict.
This distinction matters because it reframes the problem. Decisions are almost always made without proof; that has never been the issue. The question is whether the system has the capacity to hold uncertainty without immediately converting it into suppression.
Let’s examine what happens when that capacity is missing.
Suppression before proof: The behavior that drives false declines
False declines are the outcomes that everyone recognizes. They are visible, measurable, and painful. Customers abandon, and revenue is lost. Teams respond by tuning thresholds, adding rules, or increasing friction, often with diminishing returns.
But false declines are not the root behavior; they’re the outcomes. The behavior that precedes them is subtler and far more difficult to observe. We identify it as suppression before proof: the systematic suppression of legitimate activity before evidence of fraud exists, driven by uncertainty being operationally treated as risk. This distinction is not semantic; it’s structural. Its impact extends beyond visible declines.
Suppression before proof occurs upstream of outcomes. It happens at the moment of decision, when confidence is incomplete, and the system has limited expressive options. Transactions are blocked, delayed, or burdened with friction not because they’re fraudulent, but because the system can’t tolerate ambiguity.
For practitioners, this behavior feels like constant motion without resolution. Thresholds are debated. Edge cases multiply. Manual review queues fill with transactions that seem off, but not clearly wrong. Teams stay busy, yet confidence doesn’t improve. The system appears stable, while the sense that revenue is being lost in unseen ways never fully disappears.
Crucially, many suppressed transactions never register as declines at all. Customers simply abandon and retry elsewhere. From the system’s perspective, nothing happened. From the business’s perspective, revenue quietly disappeared.
This is why outcome-based dashboards undercount the cost. False declines measure what was explicitly rejected. Suppression before proof accounts for what was never allowed to exist to begin with. Because it often produces no explicit decline or recorded outcome, it remains largely invisible to traditional fraud metrics and dashboards. It lives in the gap between intent and outcome, where legitimate demand evaporates without leaving evidence behind.
It is worth acknowledging that suppression is not chosen arbitrarily. More expressive decisioning carries real costs: tighter latency budgets, deeper data dependencies, and greater operational complexity. Simpler systems are often adopted for defensible reasons. The problem isn’t that these tradeoffs exist, but that when uncertainty can only be expressed through suppression, those tradeoffs compound silently until they begin shaping outcomes that teams can no longer see or explain.
Understanding suppression before proof as a broader phenomenon, and not merely a decline problem, is essential. Without that distinction, efforts to reduce false declines will continue to treat symptoms, while the structure that produces them remains intact.
What real customers do when the systems hesitate
Suppression before proof is easy to describe from the inside. It’s far harder to observe externally, because much of its impact occurs before any explicit failure is recorded. Customers don’t file disputes or escalate. They simply abandon the attempt and take their business to a competitor. To understand how often this happens and how behavior changes as a result, we asked consumers directly about their recent purchase experiences.
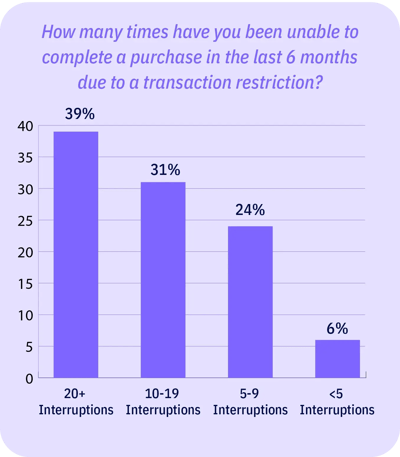
In our global consumer survey (n=1,033), checkout interruptions due to transaction restrictions were the norm, not the exception. For 95% of our respondents, they’ve experienced 5 or more interruptions in just the last 6 months, with 39% reporting being blocked 20 or more times. For most consumers in this dataset, interruption is not a one-time failure; it’s a repeated condition that shapes behavior over time.
When interruption becomes routine, consumers adapt. Most of our respondents reported switching payment methods or identities to complete a purchase, and a meaningful share went further by changing how fulfillment happens (e.g., forwarding services and third-party logistics). The result is a quieter but compounding cost: friction shifts demand into workarounds that are harder to measure and riskier to manage.

Some of these behaviors overlap with known fraud signals. The point is not that they’re risk-free, but that they’re learned responses by legitimate customers, introduced by repeated interruption rather than malicious intent.
These adaptations are not occurring in the absence of controls. Our respondents reported encountering restrictions and step-up checks that map directly to common fraud containment strategies.
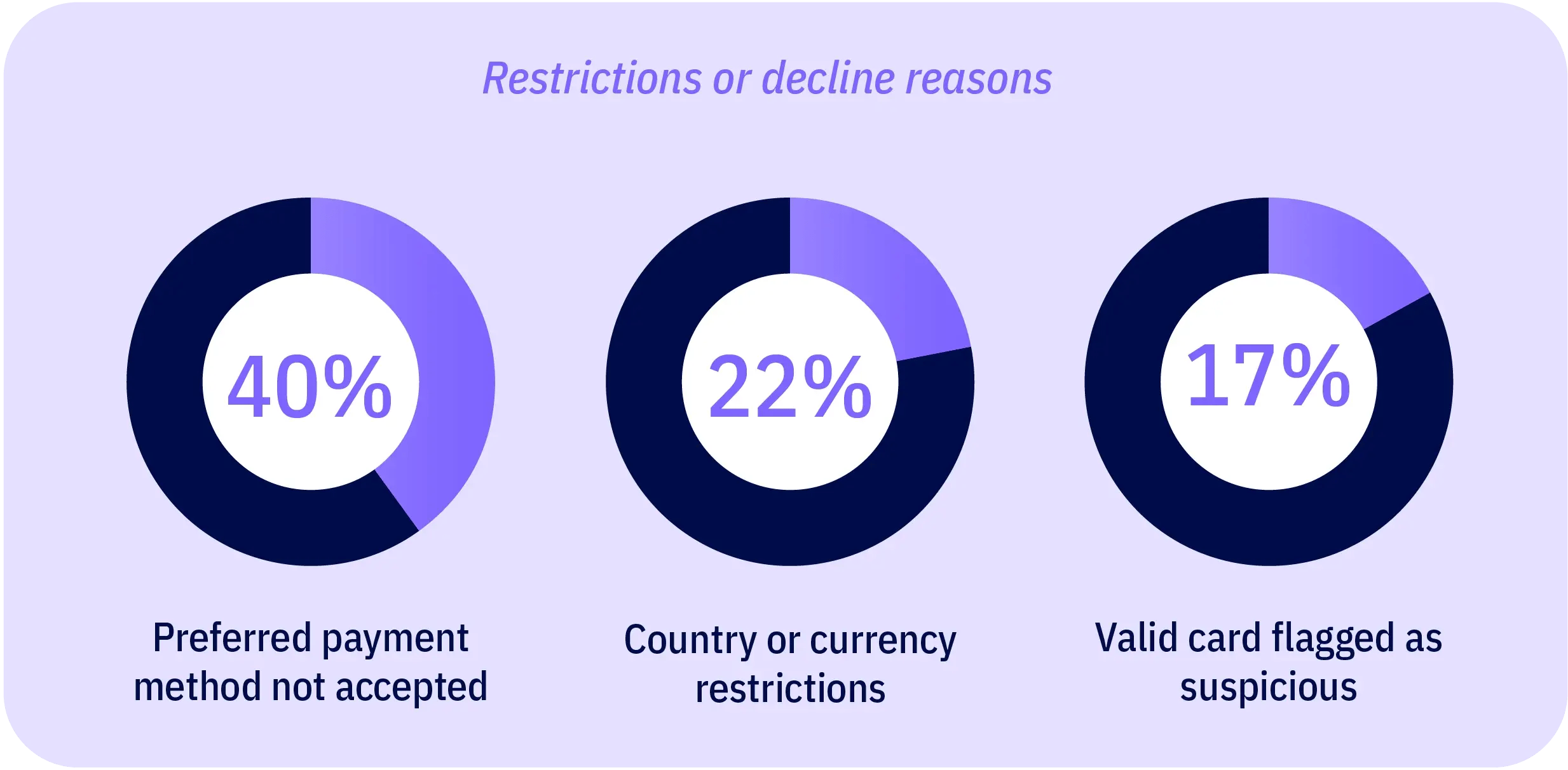


From a system perspective, these steps register as security. From a customer perspective, they register as interruption, and over time, that interruption reshapes where and how people choose to transact. What systems experience as control, customers experience as hesitation, a sign that it may be easier for them to do business elsewhere.
That reshaping translates into measurable reallocation of demand. Sixty-nine percent of respondents reported switching to a competitor or local alternative due to transaction barriers, with nearly 20% doing so often. This is not simply a failed attempt. It reflects a learned routing decision: which platforms to trust, and which to avoid.
What makes this particularly consequential is that the demand being suppressed is not marginal, and its impact isn’t confined to just ecommerce merchants. If transaction restrictions were resolved, nearly 9 in 10 of our surveyed consumers say they would shop online more, with about one-third projecting a 50+% increase.

This demand that is lost at checkout becomes a payments ecosystem issue: merchants lose conversions, payment platforms lose processing volume and introduce more edge-case flows, and card issuers and acquirers absorb higher operational load as customers retry or reroute to alternate instruments, and generate noisier signals for risk decisioning. This doesn’t prove causation in isolation, but the pattern is consistent: repeated interruptions fragments identity continuity and quietly caps legitimate commerce.
This is the operational paradox at the heart of suppression before proof. Controls designed to manage uncertainty can also increase it by teaching legitimate customers to behave in ways systems are less prepared to recognize.
Next, we’ll look at how this paradox becomes economically visible at scale, when unfamiliar behavior spikes not because fraud has increased, but because legitimate demand has been forced to route around the system.
What happens to legitimate demand under peak volatility
Peak ecommerce events don’t simply increase traffic; they change the composition of demand. They’re often dismissed as exceptions, but in practice, they’re the only moments when systems are forced to reveal how they behave at scale, when assumptions no longer hold.
During these events, legitimate customers behave differently. They shop from new locations, use unfamiliar devices, transact across borders, respond to time-bound promotions, and adopt alternative payment methods under urgency. These shifts aren’t necessarily anomalies; they’re predictable responses to scale, time pressure, and global demand concentration.
To illustrate this shift, we examined the transaction volume flowing through the Elephant Trust API across a broad cross-section of global ecommerce merchants during the Black Friday to Cyber Monday weekend, arguably the busiest shopping period of the year. Total transaction traffic increased 73% week over week. But what matters is how that growth is distributed across trust profiles. Trusted traffic surged 85%, while risky traffic only grew 36%. In absolute terms, fraud attempts did increase, but they were overwhelmed by a far larger influx of legitimate customers.
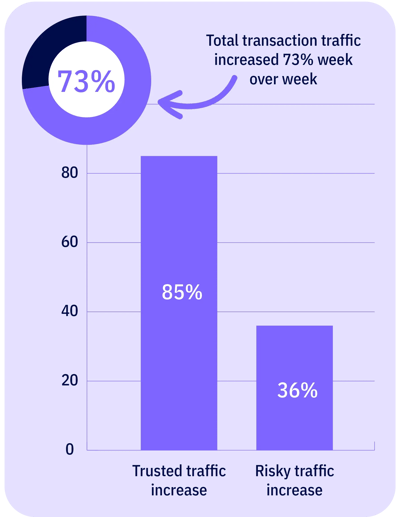
That imbalance becomes more pronounced when viewed through value, not volume. During the same period, the dollar value of trusted transactions increased 52%, compared to just 19% growth in risky transaction value. In other words, the fastest-growing segment of this holiday weekend demand was not marginal or ambiguous; it was demonstrably legitimate, revenue-bearing activity.
This matters because peak-period systems are rarely calibrated for asymmetric growth. Controls designed to manage incremental risk behave very differently when legitimate demand expands more than twice as fast as risky demand. Under those conditions, the cost of suppression rises sharply. Every conservative response disproportionately affects the segment carrying the most economic value.
The effect is especially visible when examining behaviors typically classified as high risk. Across the same Black Friday to Cyber Monday window, the firing of one signal class historically associated with elevated fraud risk increased 90% week over week across multiple industries. Signals like this are often treated as early indicators of rising fraud pressure, particularly during periods of volatility.
But when transaction outcomes were examined within this typically risky behavioral segment, the interpretation changed. Transactions within this segment generated approximately $12M in trusted transaction value, compared to $5M in risky value during the same time period. That is more than a 2.4x imbalance in favor of legitimate revenue within a category many systems treat as high risk by default.
This inversion is the core economic signal. Under peak volatility, unfamiliar behavior was not a primary fraud problem. It was a demand-routing problem. The contrast matters. Broad legitimate demand surged across industries, while meaningful fraud escalation was narrow, localized, and behaviorally distinct.
This concentration is most visible in isolated events rather than system-wide deterioration. For example, in the travel sector, a single global airline accounted for the majority of anomalous suspicious activity during the Black Friday to Cyber Monday window, experiencing a 585% increase in suspicious transactions driven by a coordinated, zero-dollar credential-testing event. The activity was sharp, intentional, and economically contained. It did not reflect a broad degradation in transaction quality across industries.
Outside of these isolated pockets, demand patterns told a different story. Legitimate customers continued to transact at scale, often through behavioral paths that appeared less familiar to static risk models but were nonetheless tied to real purchasing intent. The data does not suggest that fraud pressure increased uniformly. It suggests that the distribution of fraud diverged from the distribution of demand.
What our data reveals, then, is not a system under generalized attack, but a system operating in an environment where legitimate demand and fraud no longer scale together. When volume surges, risk becomes more unevenly distributed, while demand becomes more behaviorally diverse.
That divergence sets the conditions for suppression before proof, even when no obvious failure is visible. The cost does not announce itself as loss. It accumulates quietly, embedded in which transactions are optimized to recognize and which forms of legitimate demand remain harder to interpret at scale.
The cost that produces no evidence
The losses described previously don’t register as failure because they don’t take the form of events. Suppression before proof produces no alerts, declines, or incidents, only absence. Instead, it’s a transaction that never completes or a customer who drops before risk is expressed. From the system’s perspective, nothing happened. This isn’t an execution gap; it’s a limitation of observation.
Traditional fraud and risk systems are designed to act on risk only after it has expressed itself, and to learn from outcomes that leave a trace behind. They can infer risk from behavior that is observed, flagged, or reversed. They cannot learn from participation that exits before expression. Suppression before proof produces no artifact, no label, and no feedback signal that the system can absorb.
This creates a fundamental asymmetry in how systems learn. Fraud eventually reveals itself through impact: chargebacks, abuse patterns, and confirmed loss. Legitimate intent often does not. Risk systems learn aggressively from harm, but weakly or not at all from prevented participation. Over time, that imbalance compounds. Systems become increasingly sensitive to the behaviors that leave evidence, while remaining blind to the value that disappears quietly upstream.
This asymmetry is reinforced not just by system design but by organizational incentives. Suppression is safer to defend than uncertainty, because false positives rarely escalate, while false negatives do. As a result, teams are often rewarded for stability, even when that stability quietly constrains participation upstream.
As demand becomes more behaviorally diverse, this constraint grows more pronounced. Legitimate customers increasingly resemble edge cases rather than the norms, while fraud remains concentrated in narrower, more repeatable patterns. The system is optimized to recognize what escalates, not what exits. Stability in loss metrics reflects what the system can see, not what it may have constrained before expression.
Because this loss leaves no trace, it’s often borne unevenly; by international customers, first-time buyers, or users operating outside dominant behavioral norms, without ever registering it as a problem the system was designed to see.
This is why even well-tuned, best-in-class environments can experience meaningful erosion without visible degradation. The system continues to perform as designed, while revenue routes away through channels it was never built to observe or learn from.
The limitation is structural, not technological. As long as success is evaluated by the absence of bad outcomes, any loss that occurs before an outcome exists will remain unseen. The question is not whether existing systems should have caught the problem. It’s whether a system optimized for expressed outcomes can ever account for value that disappears before an outcome exists.
That question defines where we go next.
What mature systems optimize for next
Suppression before proof is not a symptom of weak fraud controls. It’s what emerges because fraud controls mature.
As systems improve at detecting and containing fraud, the marginal gains from further loss reduction flatten. Risk remains present, but it’s no longer the dominant source of unrecovered value. At that point, teams encounter a different kind of constraint: decisions stall not because exposure is high, but because confidence is insufficient.
This transition is increasingly explicit among mature platforms. In a recent conversation with a global travel company, they described reaching the limits of their fraud optimization. Loss had been driven down to the point where further improvements offered diminishing returns. Their focus shifted from blocking more fraud to understanding how much revenue was being lost to false declines and abandonment, value that never surfaced as failure, but was suspected to be substantial. They identified this as their largest area of potential growth.
That shift reflects a broader pattern. Even as synthetic fraud becomes more sophisticated, uncertainty increasingly governs system behavior. Rising fraud pressure amplifies ambiguity in legitimate behavior, forcing systems to become more conservative. In these environments, fraud and suppression are no longer opposing forces; they become coupled. The more ambiguity the system encounters, the more uncertainty becomes the throttle–shaping approval rates, step-up frequency, and abandonment–determining how much legitimate participation is allowed through.
Most systems were never designed to manage uncertainty explicitly at decision time, so it’s handled implicitly, through suppression rather than calibration. Tuning can reduce exposure, but it can’t expand what the system is capable of expressing. Fraud may be controlled, but meaningful value remains inaccessible.
The missing optimization is not a better prediction of what could go wrong. It’s the ability to establish confidence early enough that uncertainty doesn’t default to suppression.
Here, confidence doesn’t mean certainty, approval, or prediction of success. It refers to the system's ability to proceed with a decision despite unresolved uncertainty, based on accumulated evidence that the same real participant remains coherent across identity, context, and time. Confidence is not an outcome; it's a condition that allows the system to act without default hesitation.
This evidence doesn’t resemble traditional fraud signals. It doesn’t spike, trip thresholds, or announce itself through anomalies. Instead, it grows quietly, answering a different question; not “is this risky?”, but rather, “does this behavior make sense for this same participant over time?”
When systems rely exclusively on expressed behavior within a single interaction, they are forced to wait. By the time outcomes confirm legitimacy, participation may already have exited. Evidence that could support continuity across identity and context may be present before outcomes are known. In many environments, this evidence is fragmented, incomplete, or inaccessible at decision time. The limitation is not that continuity signals universally exist, but that most systems were never designed to assemble or reason over them early enough to influence the decision itself.
When confidence moves earlier, the system’s behavior changes. Suppression becomes less necessary, not because risk disappears, but because uncertainty is no longer the dominant constraint. At that point, the defining question shifts: not how much risk the system can block, but how much certainty it’s willing and able to tolerate while still enabling participation.
Where this leaves mature teams
Suppression before proof is not a failure of discipline or intent. It’s the natural outcome of systems that were never designed to operate under sustained uncertainty. As payment environments become more volatile, behaviorally diverse, and globally interconnected, that limitation becomes harder to ignore. Mature teams encounter it not because their controls are weak, but because their systems have reached the ceiling of what they can express.
At that point, the work changes. The question is no longer how to block more fraud or tune thresholds more precisely. The question is whether the system itself can proceed confidently when outcomes are not yet known; whether it can tolerate ambiguity without collapsing participation, and establish confidence early enough to prevent legitimate demand from silently dropping off and unnecessary friction ever being introduced.
For teams at this stage, evaluation must move upstream. Not toward new rules or more signals, but toward the capabilities a system must have to function in modern payment environments. Can it distinguish unfamiliar behavior from untrustworthy in real time? Can it assemble confidence from continuity across identity, context, and history rather than waiting for incidents to leave a trace? Can it adapt as behavior changes, without requiring manual intervention or post-hoc correction?
These are not philosophical questions. They are design tests, and they cannot be answered by intent alone. Acting on this shift is not trivial; it often requires changes to data access, learning cadence, and how confidence is governed across teams.
What this report makes clear is that a better system is possible, one that treats confidence as first-class input, learns continuously as new information appears, and allows legitimate participation to proceed without default hesitation. For teams feeling the limits of their current approach, the responsible next step is not agreement, but investigation: understanding whether the systems they rely on today were ever built to operate beyond those limits. At this stage, investigation is not premature. It’s overdue.




